Explore Security Vulnerability Trends using your GitHub data
Security Vulnerability Trends with GitHub Data
Security Vulnerability Trends analysis is crucial for GitHub users because repositories contain rich security data that directly impacts development velocity and risk management. GitHub's security alerts, dependency vulnerabilities, and code scanning results provide detailed insights into how to reduce security vulnerabilities across your codebase. This data helps engineering teams prioritize remediation efforts, identify patterns in vulnerability introduction, and measure the effectiveness of security initiatives over time.
Understanding why are security alerts increasing requires analyzing trends across repositories, dependencies, severity levels, and resolution times. GitHub users can leverage this analysis to make informed decisions about resource allocation, establish security SLAs, and demonstrate security posture improvements to stakeholders.
However, manually analyzing security vulnerability trends is incredibly painful. Spreadsheets become unwieldy when exploring multiple dimensions like repository health, alert types, and time periods—with countless permutations to track and high risk of formula errors that could misrepresent critical security data. GitHub's built-in security reporting provides basic metrics but lacks the flexibility to segment by team ownership, correlate with deployment frequency, or answer nuanced questions like "which repositories show improving security trends after implementing new scanning tools?"
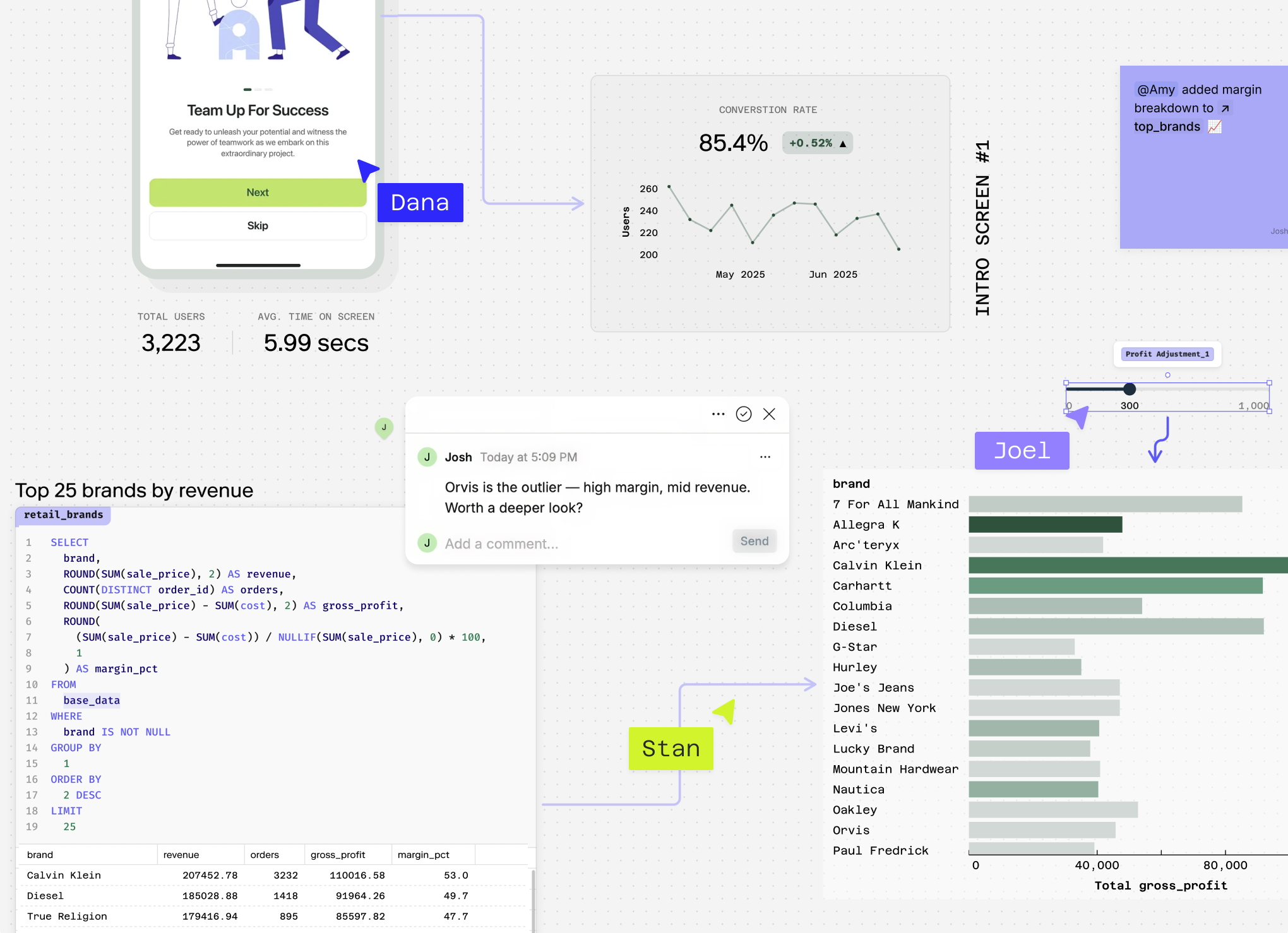
Count transforms GitHub's security data into actionable insights, enabling teams to identify vulnerability patterns, track remediation progress, and optimize their security workflows without manual data wrestling.
Stop reading about vulnerabilities. Start analyzing them.
Connect your GitHub data to Count's AI-powered canvas and actually explore those security patterns with your team in real-time.
Questions You Can Answer
What's my current security vulnerability count across all repositories? This gives you a baseline understanding of your overall security posture and helps identify which repositories need immediate attention.
Why are security alerts increasing in my main production repositories over the past quarter? This reveals patterns in vulnerability introduction, whether from new dependencies, code changes, or external threat discoveries, helping you understand root causes.
How to reduce security vulnerabilities by comparing resolution times across different severity levels? Analyzing critical vs. high vs. medium severity alert resolution patterns shows where your team's triage process is most effective and where improvements are needed.
Which developers or teams have the fastest security alert resolution rates, and what repositories do they work on? This identifies security champions within your organization and best practices that can be shared across teams to improve overall response times.
How do security vulnerability trends correlate with deployment frequency and repository activity levels? This sophisticated analysis reveals whether faster development cycles introduce more security risks, helping you balance velocity with security in your development process.
What's the relationship between dependency update frequency and new security alerts by programming language? This cross-cutting analysis helps you understand how different tech stacks and maintenance practices affect your security vulnerability landscape.
How Count Does This
Count's AI agent creates bespoke analysis tailored to your specific security questions — whether you're investigating how to reduce security vulnerabilities across specific repositories or understanding why are security alerts increasing in your organization. Instead of rigid templates, Count writes custom SQL and Python logic that adapts to your unique GitHub security data structure and business context.
Count runs hundreds of queries in seconds to uncover hidden vulnerability patterns — automatically correlating alert types with repository activity, developer commits, and dependency updates to reveal insights you'd miss with manual analysis. The platform handles messy GitHub data by cleaning inconsistent alert classifications, normalizing repository metadata, and resolving duplicate security findings across your organization.
Every analysis includes transparent methodology — Count shows exactly how it calculated vulnerability trends, which repositories were included, and what assumptions were made about alert severity scoring. This ensures your security team can verify and trust the results when presenting to stakeholders.
Count delivers presentation-ready security reports that transform raw GitHub security data into executive-level insights about vulnerability exposure and remediation progress. The collaborative environment lets your security and development teams explore results together, ask follow-up questions about specific vulnerabilities, and coordinate remediation efforts.
Multi-source analysis connects GitHub security data with your incident management tools, deployment pipelines, and business metrics — helping you understand how security vulnerabilities impact overall development velocity and customer experience.
Explore related metrics
Stop reading about vulnerabilities. Start analyzing them.
Connect your GitHub data to Count's AI-powered canvas and actually explore those security patterns with your team in real-time.