Explore Security Alert Resolution Time using your GitHub data
Security Alert Resolution Time in GitHub
Security Alert Resolution Time measures how quickly your development team addresses and resolves security vulnerabilities identified in your GitHub repositories. For GitHub users, this metric is particularly valuable because GitHub's security advisory database, Dependabot alerts, and code scanning tools generate rich data about vulnerability discovery dates, severity levels, affected repositories, and resolution timestamps. This information helps engineering leaders understand how to reduce security alert resolution time by identifying bottlenecks in their security response process and prioritizing high-impact vulnerabilities.
GitHub's comprehensive security data enables teams to analyze resolution patterns across different repositories, vulnerability types, and team members. You can identify which types of alerts take longest to resolve, whether critical vulnerabilities receive appropriate priority, and how resolution times correlate with repository activity levels. This analysis directly informs decisions about resource allocation, security tooling investments, and process improvements.
However, analyzing this data manually creates significant challenges. Spreadsheets quickly become unwieldy when exploring multiple dimensions like severity, repository, assignee, and time periods—leading to formula errors and hours of maintenance work. GitHub's built-in security reporting provides basic metrics but lacks the flexibility to segment data meaningfully or answer specific questions like "why is security alert resolution time high for our mobile repositories compared to backend services?"
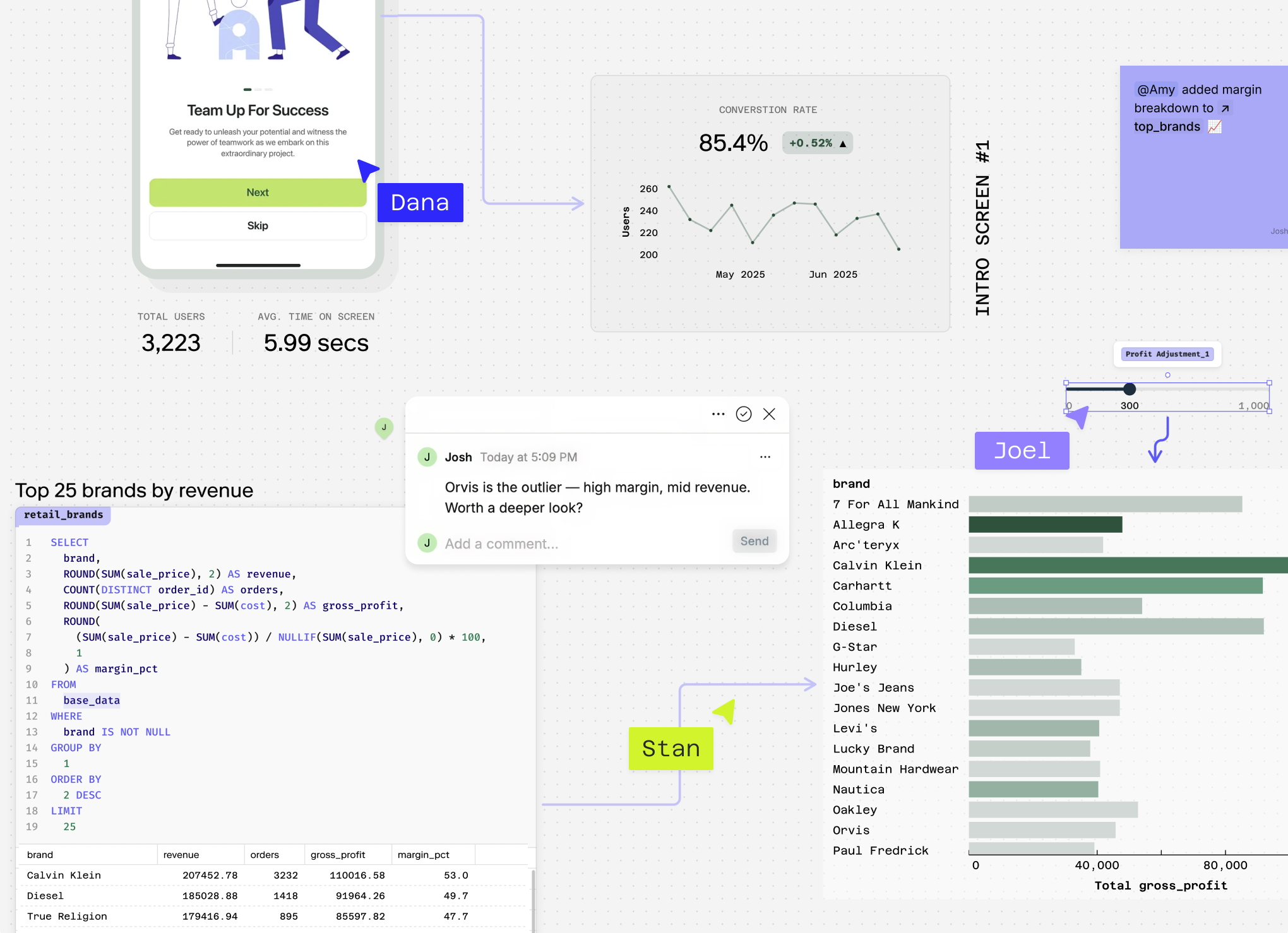
Count transforms your GitHub security data into actionable insights, enabling deep analysis without the manual overhead of spreadsheet management or the limitations of GitHub's standard reporting tools.
Ready to actually analyze your security response times?
Connect your GitHub data and warehouse in Count's AI-powered canvas. See patterns, write queries, and collaborate with your team in real-time.
Questions You Can Answer
What's our average security alert resolution time across all repositories? This foundational question provides a baseline understanding of your team's overall security response performance, helping you establish benchmarks for improvement.
Why is security alert resolution time high for critical severity alerts? By filtering for critical alerts, you can identify bottlenecks in your most urgent security processes and understand what factors contribute to delays in addressing high-priority vulnerabilities.
How to reduce security alert resolution time by repository owner or team? Segmenting resolution times by repository ownership reveals which teams or maintainers consistently resolve alerts faster, allowing you to identify best practices and training opportunities across your organization.
What's the trend in security alert resolution time over the past 6 months by alert type? This temporal analysis helps you understand whether your security processes are improving over time and identifies seasonal patterns or specific vulnerability types that consistently take longer to address.
How does security alert resolution time correlate with repository activity levels and pull request frequency? This sophisticated cross-analysis reveals whether more active repositories resolve security alerts faster due to increased developer attention, or slower due to competing priorities, informing resource allocation decisions.
Which programming languages in our repositories have the longest security alert resolution times? Language-specific analysis helps identify technology stacks that may need additional security tooling, training, or dedicated expertise to improve vulnerability response times.
How Count Analyses Security Alert Resolution Time
Count's AI agent goes far beyond basic GitHub security metrics by writing custom analysis code tailored to your specific security questions. Instead of using rigid templates, Count crafts bespoke SQL and Python logic to understand why is security alert resolution time high in your repositories and how to reduce security alert resolution time effectively.
When you ask about security performance, Count runs hundreds of queries in seconds to uncover hidden patterns in your GitHub data. It might segment your security alert resolution time by repository size, alert severity level, team assignment, and time of detection in a single comprehensive analysis — revealing insights like slower resolution times for alerts discovered during weekends or critical vulnerabilities taking longer in larger codebases.
Count automatically handles messy GitHub data, cleaning away incomplete alert records or inconsistent timestamps that would derail manual analysis. Every methodology is transparent — you can verify how Count calculated resolution times, handled overlapping alerts, or weighted different severity levels.
The platform delivers presentation-ready analysis that transforms your security questions into actionable insights. Count might discover that high-severity alerts in Node.js repositories take 40% longer to resolve than similar alerts in Python projects, complete with visualizations and recommendations.
Count's collaborative features let your entire security team explore results together, asking follow-up questions like "Which developers resolve alerts fastest?" Count also connects GitHub security data with your incident management systems or deployment logs, providing holistic analysis of how security alert resolution impacts your overall development velocity and system reliability.
Explore related metrics
Ready to actually analyze your security response times?
Connect your GitHub data and warehouse in Count's AI-powered canvas. See patterns, write queries, and collaborate with your team in real-time.